In today's connected world, a company's network is super important. It's how data moves, how people get to programs, and how business gets done. But this setup is also a target for cybercriminals. They're always looking for weak spots to break in, steal data, mess things up, and make money.
So, protecting these networks is key. A network security assessment is a way to find problems early, figure out the risks, and get advice on the best defenses. This keeps a company's digital stuff safe from the latest threats.
What Is Network Security Assessment?
A network security assessment is when you look at a company's computer networks to find possible problems. It's more than just a quick scan for known issues. It looks closely at how things are set up, the rules for communication, security plans, and even how employees handle security. This gives a full understanding of how safe the network is. It helps find flaws before bad guys do, and it gives a complete view of the company's network defenses.
The assessment covers a lot of ground. It looks at firewalls, routers, switches, security systems, Wi-Fi, servers, computers, and even connected gadgets. The goal is to find things like wrong settings, old software, weak passwords, and any holes that could let someone in to steal stuff or cause trouble. It's about knowing all the ways an attacker might try to get in.
The final aim is to give a clear idea of a company's security strengths and weaknesses. It's not just about following rules. It's about giving useful advice on what to fix first. By knowing where the problems are and how bad they could be, companies can decide where to spend money on security, make their defenses stronger, and lower the risk of cyberattacks. This keeps their important network stuff safe and working right.
Key Aspects of Network Security Assessment
A network security assessment needs to be done right. It's not just about finding technical problems. It also means looking at how the network is set up, the security plans, how the company responds to problems, and if employees know about security. This helps find bigger problems that a simple scan might miss.
It also means using both computer programs and experts. Programs can find many common problems quickly, but they don't always understand the situation or think like a hacker. Experts can figure out tricky problems and copy real attacks that programs might not catch. Together, they give a better view of how strong the network is.
The assessment should also give clear advice on what to fix first. It shouldn't just list problems. It should say how to fix them and which ones are most important. This helps companies spend their time and money wisely to get the best security improvements.
Why Is Network Security Assessment Important?
Network security assessments are super important because cyberattacks are getting more common and harder to stop. Companies are always at risk of having data stolen, being held for ransom, getting attacked to shut them down, or having their ideas stolen. Without regular assessments, problems can stay hidden and let attackers into important systems. Checking early is now a must for staying safe in the digital world.
Also, assessments are needed to follow the rules. Many industries have rules about protecting data and staying secure, like GDPR, HIPAA, PCI DSS, and ISO 27001. These rules say companies must do regular security checks. If they don't, they can get big fines and lose their certifications. So, companies need to show they're doing their best to keep their networks safe.
Besides following rules and stopping attacks, good network security helps build trust with customers, partners, and investors. They want to know their data is safe. By doing regular assessments and fixing problems, companies can show they're serious about security. This improves their reputation and gives them an edge over competitors.
How Does a Network Security Assessment Work?
A network security assessment usually follows a plan to make sure everything is covered and the results are useful. First, the people doing the assessment figure out what to look at. They find the important stuff and learn about the network, programs, and security that's already there. This might mean mapping the network, scanning for open doors, and finding out what's visible from the outside.
Next, they look for problems. They use programs to scan for known weaknesses and also check things by hand. Experts try to get around the security and look for mistakes that programs might miss. They might even try to break into the system in a safe way to see how bad the problems are.
Finally, they write a report with all the problems they found, how bad they are, and how to fix them. The report gives advice to the IT team and a summary for the bosses. The assessment team might also help with fixing the problems and making sure the fixes worked. This makes the network stronger.
Types of Network Security Assessments
There are different types of network security assessments, depending on what you want to achieve:
A weakness assessment looks for security problems in a network, system, or program. It mostly uses programs to find known problems and weak settings. It gives a list of problems and how bad they are, but it doesn't try to break in. It's good for regular checks to make sure basic security is in place.
A break-in test goes further than a weakness assessment. It tries to break into the system to see if someone can get unauthorized access. Experts copy real-world attacks to get past security and steal data. Break-in tests can be done from outside the company (like from the internet) or from inside (like by a bad employee). This shows what an attacker could really do.
There are also assessments for specific things. A Wi-Fi security assessment looks for problems in wireless networks. A settings review checks the security settings on network devices and programs. A social engineering assessment tests how easily employees can be tricked into giving away information. The type of assessment you choose depends on what you want to achieve and how much risk you're willing to take.
Components of a Network Security Assessment
A network security assessment looks at several important parts of a company's digital stuff.
First, it looks at the network itself, including firewalls, routers, switches, and Wi-Fi. Experts check these devices for wrong settings, weak passwords, open ports, and old software. They also check the security rules to make sure they're strict enough to block unauthorized access.
It also looks at the security of servers and computers. This includes checking for missing security updates, weak passwords, and problems in programs. Security programs like antivirus are also checked to make sure they're working right.
Finally, the assessment looks at security plans and how employees handle security. This means checking security policies, incident response plans, and who has access to what. It also looks at whether employees are trained to avoid getting tricked. Having strong security measures, good plans, and trained employees makes the network more resilient.
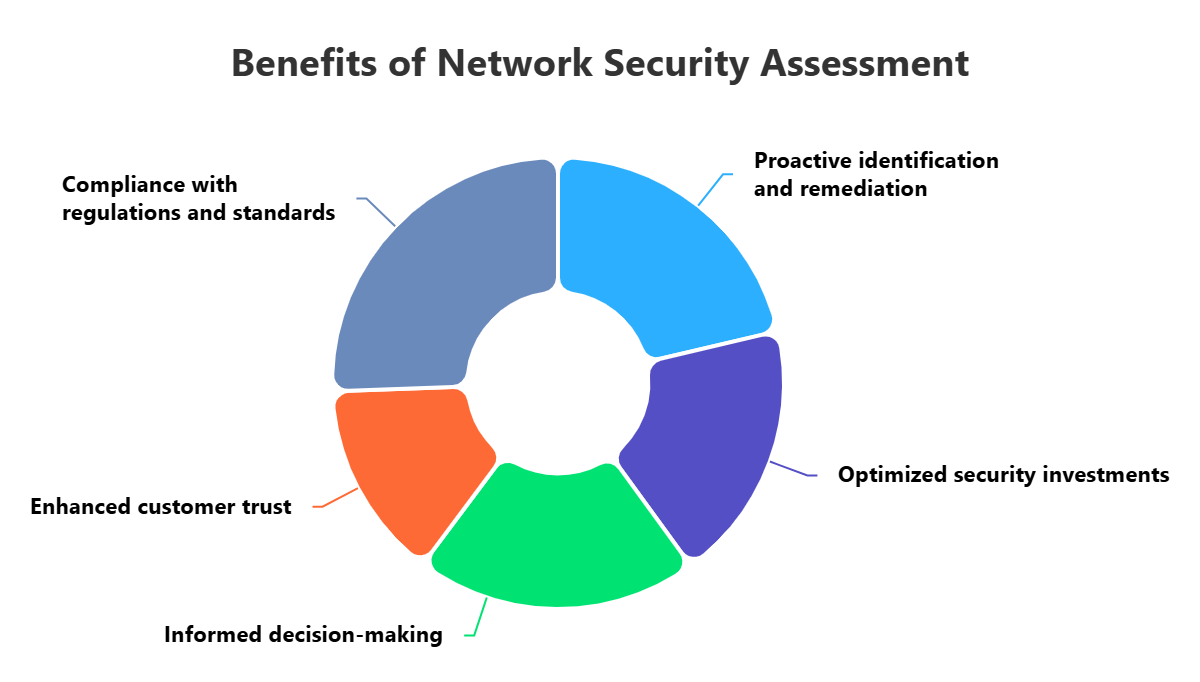
Benefits of Network Security Assessment
Doing regular network security assessments has many benefits for companies. It helps find and fix problems before they're used by attackers. By copying real-world attacks, assessments find weaknesses that might be missed. This lets companies fix systems and strengthen security, which lowers the risk of attacks, data theft, and downtime.
Assessments also help companies follow the rules. Many regulations say companies must do regular security checks. By doing these assessments, companies can show they're protecting data and avoiding fines.
Besides improving security and following rules, assessments help companies make smart decisions about security. The reports give a clear idea of the company's security risks. This helps managers decide where to spend money and what to focus on to get the best security improvements.
Challenges of Network Security Assessment
Network security assessments have some challenges. One big problem is that networks are always getting more complex. Companies have systems in their offices, in the cloud, and used by remote workers. This makes it hard to check everything and keep up with changes.
Another challenge is balancing being thorough with not causing problems. Deep assessments can find important problems, but they can also disrupt systems. Companies need to be careful about how they test things to avoid causing downtime.
Finally, it's hard to find skilled security people and keep up with the latest threats. Assessments need people who know a lot about networks, security tools, and attacks. Also, attackers are always coming up with new tricks, so security teams need to keep learning.
Best Practices for Network Security Assessments
To get the most out of network security assessments, follow these best practices:
First, be clear about what you're checking. Know what systems are included, what you want to achieve, and how you're going to do it. This makes sure everything important is covered.
Second, focus on the most important problems and give clear advice on how to fix them. Don't just list problems. Explain how bad they are and how to fix them. This helps IT teams know what to do first.
Finally, make assessments a regular part of your security plan. Security is not a one-time thing. Do assessments regularly and encourage security teams, IT teams, and developers to work together. This makes sure problems are found, understood, and fixed quickly.
How ImmuniWeb Can Help with Network Security Assessment?
Discover your externally accessible network devices and services with ImmuniWeb® Discovery network security assessment offering. Just enter your company name to get a comprehensive visibility of your external servers, network and IoT devices, and other IT assets hosted both on-premise and in a multi-cloud environment. The network security assessment offering is bundled with our award-winning attack surface management technology to ensure that all your network services are detected and assessed, including shadow IT and shadow cloud infrastructure that may lead to disastrous data breaches.
During the non-intrusive network security assessment, every open network port is carefully analyzed with our smart fingerprinting technology to detect the running network service and its version to provide you with a risk-based scoring for each of your network IP address. Unlike the traditional network vulnerability scanning solutions, our production-safe network scanning technology will not disrupt or slow down your network services, while getting all the information you need.
Detect shadow, abandoned or forgotten servers and network equipment with critical vulnerabilities. Reduce your network attack surface to accelerate and cut the costs of network penetration testing or PCI DSS scanning. Dispatch instant alerts to the relevant people in your team by using groups, tags and alerts on the interactive dashboard. Export vulnerability data via the API into your SIEM or simply get the findings in a PDF or XLS file. Enjoy a fixed monthly price per company regardless the number of network assets and services.
Disclaimer
The above-mentioned text does not constitute legal or investment advice and is provided “as is” without any warranty of any kind. We recommend talking to ImmuniWeb experts to get a better understanding of the subject matter.











