As more companies move to cloud computing, keeping those cloud setups secure becomes a joint effort. Cloud providers handle security “of” the cloud, but customers are in charge of security “in” the cloud. This change has led to the rise of Cloud Security Posture Management (CSPM), which is key for staying secure in today's changing cloud world.
What Is Cloud Security Posture Management?
Cloud Security Posture Management (CSPM) is like having an automated system that watches, finds, and fixes security problems and rule breaks in your cloud setup. It looks for things like wrong settings, policy issues, and weak spots in different cloud services, like Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and sometimes Software as a Service (SaaS). The main goal of CSPM is to give companies a live view of their cloud security and make sure their cloud stuff follows security rules and laws.
Normal security tools often can't keep up in cloud environments because things change so fast and there's so much to keep track of. CSPM tools fix this by connecting right to cloud provider systems (like AWS Config, Azure Policy, and GCP Cloud Asset Inventory) to grab settings data all the time. This way, CSPM can create a big list of all your cloud stuff and check it against security rules, industry standards (like CIS Benchmarks), and legal needs.
Basically, CSPM is like a security guard for your cloud. It helps companies avoid the hassle of checking settings by hand, which takes time and can lead to mistakes. By automatically finding wrong settings—a common cause of cloud security problems—CSPM makes your cloud setup safer, strengthens your defenses, and makes it easier to follow the rules.
Key Aspects of Cloud Security Posture Management
One important thing about CSPM is that it keeps watching and giving you a live view across many clouds and hybrid setups. Cloud resources are always changing, with things being added, changed, and removed. CSPM solutions keep checking cloud provider systems to keep a current list of all your stuff, how it's set up, and its security settings. This live view lets security teams quickly spot setting changes, unauthorized actions, and new weak spots, so problems don't go unnoticed.
Another key is finding wrong settings and policy issues automatically. CSPM tools have big collections of security policies and standard rules (like CIS Benchmarks, NIST, PCI DSS, HIPAA, and GDPR). They automatically check your cloud resource settings against these standards. If something's off—like a public S3 bucket, a too-open IAM role, or unencrypted data—CSPM flags it as a possible risk and sends alerts to security teams.
Smart risk checking and ranking are also key for CSPM to work well. Not all wrong settings are equally risky. A good CSPM tool doesn't just send alerts for everything; it also looks at things like how exposed an asset is (like if it's on the internet), how sensitive the data is, and what could happen if it's hacked. This smart ranking helps security teams focus on the most important risks, use their resources wisely, and improve security overall.
Why Is Cloud Security Posture Management Important?
Cloud Security Posture Management is super important now because everyone's using cloud services, which come with their own security challenges. Cloud setups can grow fast and change a lot, which means settings can change often, leading to mistakes that cause security problems. Companies often can't see everything happening across their cloud stuff, making it hard to find and manage risks by hand. CSPM gives the automated, constant watch needed to handle these problems and prevent expensive security screw-ups.
Following the rules is another big reason why CSPM matters. Many data privacy laws (like GDPR, HIPAA, and CCPA) and industry rules (like PCI DSS and ISO 27001) demand strict security and tracking for systems that handle sensitive data. Since cloud setups often deal with this kind of data, it's vital to prove that you're always following these rules. CSPM solutions automate rule checks, match cloud settings to specific legal needs, and create reports for audits, which makes compliance easier and lowers the risk of big fines and legal trouble.
Finally, CSPM is key for being proactive and strong with cloud security. By finding and fixing wrong settings and weak spots early, CSPM saves time, money, and effort on fixing things later. It gives security and IT teams useful info, letting them automate fixes and add security to their workflows. This constant improvement makes cloud defenses stronger, reduces the attack surface, and protects important stuff.
How Does Cloud Security Posture Management Work?
A CSPM solution usually works in a few connected steps, starting with finding and listing cloud assets. CSPM tools connect right to systems from cloud providers like AWS, Azure, Google Cloud, and sometimes others. Through these connections, the CSPM solution constantly scans the company's cloud accounts to find and list all the things they're using—from virtual machines and storage to serverless functions and network settings. This creates a complete, live list of everything in the cloud, which is vital for seeing what's going on.
After finding the assets, the CSPM solution starts checking and analyzing things. It compares the settings of each cloud resource against security rules, industry standards (like CIS Benchmarks), and legal needs. The CSPM system looks for anything that's different from these standards, flagging them as wrong settings or policy issues. This analysis often involves smart ways to understand how cloud resources depend on each other and how a wrong setting in one service could affect another.
The last important steps are ranking risks, sending alerts, and guiding fixes. When wrong settings or weak spots are found, the CSPM solution ranks them based on how bad they are, how much they could affect things, and how exposed they are. Then, it sends alerts and detailed reports to security teams. These reports usually include steps to fix the problem, often with commands or settings needed to make the fix. Many CSPM tools can also fix certain wrong settings automatically based on rules, which saves time and speeds up responses.
Types of Cloud Security Posture Management
While CSPM does the same basic thing, there are different kinds of solutions based on how they're set up and what they focus on. One common difference is between Cloud-Native CSPM, which is offered by cloud providers themselves, and Third-Party CSPM solutions. Cloud-native tools (like AWS Security Hub, Azure Security Center, and Google Cloud Security Command Center) connect well with their own cloud environments and often give quick info on basic wrong settings. But they usually only work with one cloud provider, making them less useful for companies using multiple clouds.
On the other hand, Third-Party CSPM solutions work with any cloud provider (AWS, Azure, GCP, and sometimes others) and hybrid setups. These solutions give a single view and consistent rules across different cloud setups, which is important for companies using multiple cloud strategies. They often have better features like creating custom rules, connecting with other security tools, and ranking risks in smarter ways that go beyond individual cloud providers.
CSPM features are also being added to bigger Cloud-Native Application Protection Platforms (CNAPPs). CNAPPs aim to give a full view of cloud security from code to runtime, including not only CSPM but also Cloud Workload Protection Platforms (CWPP), Cloud Infrastructure Entitlement Management (CIEM), and sometimes more. While CSPM focuses on settings and compliance, a CNAPP gives a more complete security solution that includes runtime protection, workload vulnerability management, and identity control, offering a combined way to handle cloud security.
Components of Cloud Security Posture Management
A good CSPM solution has several important parts that work together to make sure cloud security is well-managed. A key part is the Cloud Asset Inventory and Discovery Engine. This part connects to cloud provider systems to constantly find, list, and track every resource used across all cloud accounts. This includes virtual machines, storage, databases, network settings, load balancers, serverless functions, and all related info. A complete and current list is vital for any security check.
Another important part is the Policy and Compliance Engine. This is where security rules and compliance standards are stored. It has a big list of security rules based on industry standards (like CIS Benchmarks, NIST, and ISO 27001), legal rules (like GDPR, HIPAA, and PCI DSS), and company practices. This engine constantly compares the settings of cloud assets against these rules. It finds any differences or wrong settings that could cause problems or non-compliance, acting as the brain for checking security.
Finally, the Risk Assessment, Alerting, and Remediation Workflow is very important. When wrong settings are found, this part ranks them based on how bad they are and what effect they could have. It sends real-time alerts to security teams through different ways (like email, Slack, and SIEM). Importantly, it gives clear steps to fix the problems, often with commands or scripts to make the fixes. Many CSPM solutions also have reporting for compliance audits and dashboards to show the overall security and progress on fixing things.
Benefits of Cloud Security Posture Management
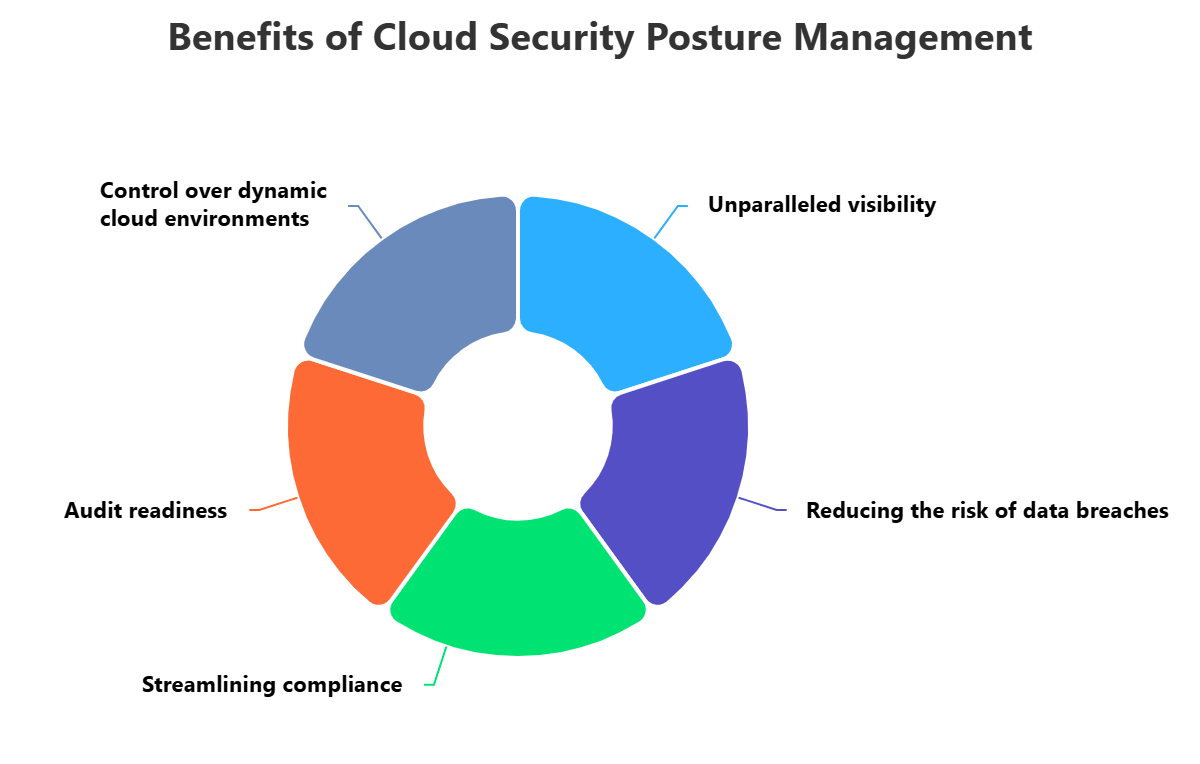
Using Cloud Security Posture Management brings many benefits that are important for any company using the cloud. First, CSPM gives great visibility and control over changing cloud setups. In complex multi-cloud or hybrid setups, it's almost impossible to manually track every resource and its settings. CSPM tools automate this finding, giving a central dashboard that shows a live, complete view of all cloud assets and their security, letting security teams find weak spots and know everything about their attack surface.
Second, CSPM greatly lowers the risk of data breaches and security issues caused by wrong settings. Wrong settings are a main cause of cloud security issues. By constantly watching settings against best practices and quickly flagging differences, CSPM lets companies find and fix these problems before attackers can use them. This proactive way lowers the chance of costly data breaches, unauthorized access, and service problems.
Finally, CSPM helps a lot in making compliance easier and getting ready for audits. Following many legal rules (like GDPR, HIPAA, and PCI DSS) can be hard for cloud setups. CSPM solutions automate compliance checks, matching cloud settings to specific legal needs and making complete reports for audits. This not only lowers the manual work for compliance but also makes sure you're always following the rules, helping you avoid penalties, build trust, and show that you're doing your best to auditors.
Challenges of Cloud Security Posture Management
Even with the benefits, using Cloud Security Posture Management can have challenges. One main problem is that cloud setups are complex and always changing. Cloud providers keep adding new services, features, and settings. Keeping CSPM rules up-to-date to cover these changes and make sure everything's checked across cloud platforms (AWS, Azure, GCP) takes constant effort and cloud knowledge, making it hard to keep security consistent.
Another challenge is dealing with too many alerts and knowing which fixes to do first. CSPM tools can send a lot of alerts, especially in big cloud setups. Many of these alerts might be for small problems or even wrong alarms, leading to alert fatigue where security teams get confused and miss important alerts. Knowing which alerts are really risky, understanding the business reasons for each wrong setting, and knowing which problems are most important takes good processes and skilled people to avoid wasting time on small fixes.
Finally, adding CSPM to existing IT workflows and making sure fixes are done can be hard. While CSPM wants security to be done early, connecting security findings with developer fixes can be a challenge. Developers might not understand the fixes or might have trouble prioritizing them while they're also building new features. Making CSPM work well with IT systems, automating fixes when possible, and encouraging teamwork between security, IT, and developers is important to make sure wrong settings are found and fixed quickly.
Best Practices for Cloud Security Posture Management
To make Cloud Security Posture Management work best, companies should use these key practices. First, have clear cloud rules and security policies before using CSPM. This means deciding your company's security basics, legal needs, and how much risk is okay for cloud resources. These policies should be made into automated rules in your CSPM tool. Review these policies often to match changes in your cloud setup, business needs, and legal changes, making sure your CSPM solution is always checking against the right standards.
Second, fix problems based on risk and automate fixes when you can. Not all wrong settings are equally important. Use your CSPM tool to find the riskiest problems that could cause the most harm (like public data or ways to get more access). For small, common wrong settings, use automated fixes offered by your CSPM solution. Automating fixes for known problems can save time, speed up responses, and let security teams focus on bigger challenges.
Finally, connect CSPM with your IT processes and encourage everyone to share security responsibility. Do security checks early by adding CSPM checks to your IT processes, making sure wrong settings are caught before code is released. This lets developers fix problems early when they're cheaper to fix. Also, teach developers, IT, and security teams about cloud security practices and shared responsibility. Encourage teamwork and shared ownership of cloud security to build a strong cloud and make security part of every step of development.
How ImmuniWeb Can Help with Cloud Security Posture Management?
Get a helicopter view on your multi-cloud attack surface with ImmuniWeb® Discovery cloud security posture management. In contrast to other vendors, you don’t need to provide us with your cloud IAM account: just enter your company name to start searching for your exposed cloud assets and endpoints of AWS, Azure, GCP and over 50 other public cloud service providers (CSP) around the globe. Detect shadow cloud resources or unwarranted cloud usage that may violate compliance requirements.
Our award-winning cloud security posture management rapidly detects your externally visible cloud assets including cloud computing instances, data storage, gateways, load balancers, databases, and various APIs or endpoints of cloud services. In addition to assessing your cloud attack surface for various misconfigurations, such as excessive access permissions or insecure IAM policies, we also visualize your geographical data storage for compliance and regulatory purposes.
Leverage our API to synchronize the cloud security posture management data flow with your SIEM or cloud-native monitoring systems, or simply export the findings into a PDF or XLS file. Enjoy a fixed monthly price per company regardless of the number of cloud assets, endpoints or security events. Customize instant alerts to relevant people in your DevOps of cybersecurity team once a misconfiguration is detected in your cloud environment.
Disclaimer
The above-mentioned text does not constitute legal or investment advice and is provided “as is” without any warranty of any kind. We recommend talking to ImmuniWeb experts to get a better understanding of the subject matter.











