Cyber threats are getting more complex, and IT is always changing. Because of this, older ways of checking security sometimes don't cut it anymore. Companies need to be ready all the time to test their defenses against attackers who keep changing their methods. That's where Continuous Breach and Attack Simulation (CBAS) comes in. It's a way to keep an eye on your security in real-time.
What Is Continuous Breach and Attack Simulation (CBAS)?
CBAS is a tool that tests your security using the same tricks that real attackers use. Unlike normal security tests that take place occasionally, CBAS works all the time. It keeps testing your whole IT system, including computers, networks, clouds, and apps, without causing any harm. The main point is to see if your current security tools and processes are doing their job.
CBAS uses a big collection of attack methods that are based on guides like MITRE ATT&CK. It acts out complete attack scenarios, from the first step to trying to steal data. Importantly, these tests are safe and don't mess up your real systems. This way, you can constantly check your defenses.
In the end, CBAS gives you a clear idea of how strong your security is. It answers questions like: can someone get past our firewall? or will our system catch this ransomware? By testing your security over and over, CBAS helps you find problems early, fix them, make the most of your security investments, and get better at defending yourself.
Why CBAS Is Important?
CBAS focuses on checking your security all the time. Normal security checks only give you a snapshot in time. CBAS is always running, so it can spot new problems as they appear, like when new weaknesses are found, settings are changed, or new devices are added. This constant testing lets you see how well your defenses are working right away.
Also, CBAS acts out full attack scenarios using real-world methods. It doesn't just look for weaknesses; it copies how attackers behave, from getting in to stealing data. It uses a collection of attack methods that is always being updated, based on guides like MITRE ATT&CK. This makes the tests very realistic and shows how well you can stand up to serious attacks.
CBAS also measures how well your security tools and teams are doing. It checks if your tools are catching attacks and if your security team is responding correctly. By running fake attacks and watching how your security systems react, CBAS gives you real numbers on how well your tools are working. This helps you spend your money on the right security and make your security team more efficient.
Why CBAS Matters?
CBAS is very important today because cyber threats are getting more advanced and IT systems are changing so fast. Normal security checks only show you what your security is like at that moment. But security is always changing, with new devices, settings, and attack methods appearing all the time. This means there can be gaps in your defenses between checks, leaving you open to attack. CBAS fixes this by testing your defenses constantly, so you can find and fix problems quickly.
Also, companies spend a lot of money on security tools. CBAS gives you a way to see if these tools are really working. It shows you if a tool can catch or stop a certain attack method, proving that it's worth the investment and helping you set it up correctly.
Finally, CBAS helps you build a strong and flexible security system. It lets your security teams be proactive, learning from fake attacks and using what they learn to improve their defenses. By finding weak spots and giving advice on how to fix them, CBAS helps you improve your security and reduce your overall risk.
How CBAS Works?
CBAS usually works through a series of steps that are automated by a CBAS platform. First, the platform finds all your IT assets and gets set up. It then finds all the devices, networks, apps, and cloud services in your system. Then, your security team tells the platform what kinds of attacks to test for, using a library of known threats.
Once it's set up, the CBAS platform starts running tests all the time. It puts small programs on your devices that act out different steps of an attack. For example, they might try to get past security on computers, move around inside your network, exploit weaknesses, or steal data. These tests are safe and don't harm your real systems. This testing runs constantly and changes as your system changes.
The last step is to check if the attacks were detected, create reports, and give advice on what to do. The CBAS platform watches your security tools to see if they catch the attacks. Then, it gives you detailed reports that show which attacks worked, which security measures were bypassed, and where the gaps are. This information is often organized using guides like MITRE ATT&CK. With this advice, your security team can fix problems, fine-tune security tools, and improve how they respond to incidents.
What Are the Types of CBAS?
CBAS platforms offer different kinds of tests for different parts of your IT system. One common type is Endpoint Security Validation, which checks how well your computer security is working. It tests things like antivirus software and firewalls. The CBAS programs on computers copy different kinds of attacks to see if the security can catch them.
Another type is Network Security Validation. This tests attacks that move across your network to see how well your firewalls and intrusion prevention systems are working. CBAS platforms might copy techniques like scanning ports or stealing data over the network. The goal is to see if your network security can catch and stop harmful activity.
Cloud Security Validation is also becoming important. It's designed for systems hosted on cloud platforms like AWS, Azure, and GCP. These tests target cloud-specific attacks, like misconfigured cloud services or weaknesses in cloud functions. This helps companies make sure their cloud security is set up correctly.
Components of CBAS
A CBAS platform has several parts that work together to test your security automatically. One key part is the Attack Simulation Engine and Scenario Library. This is the brain of the platform, containing a collection of real-world attack techniques. The engine runs the fake attacks, from simple password theft to complex attacks that involve moving around inside the network and stealing data.
Another part is the Agents or Sensors, which let the platform interact with your IT system. These are small programs installed on devices or connections to cloud and network services. They run the fake attacks, collect data on how security tools respond, and send the information back to the platform. They're designed to be safe and not slow down your system.
The Reporting, Analytics, and Remediation Orchestration module turns the test results into advice on how to improve security. It combines all the data from the attacks, compares it with alerts from security tools, and presents it in reports. It shows which attacks worked, which security measures were bypassed, and how to fix the problems.
Benefits of CBAS
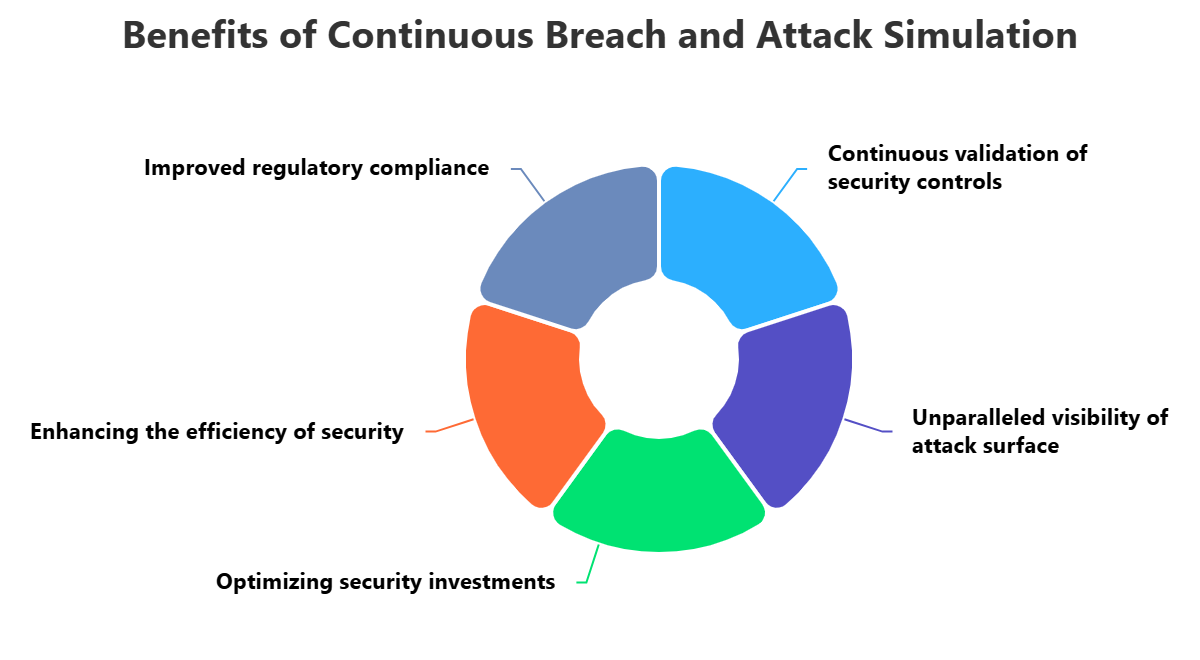
Using CBAS has many benefits that can greatly improve your security. One of the most important is that it gives you real proof of how well your security measures are working. It tests your tools and processes against real-world attacks. This testing makes sure that any gaps in your defenses are found quickly, reducing your risk.
CBAS also gives you a clear view of your cyber risk. By running attacks across your whole IT system, it finds hidden weaknesses that normal tests might miss. This helps you understand your real risks and decide where to spend your security resources.
CBAS also helps you get the most out of your security investments and make your security operations more efficient. It proves whether your security tools can catch certain attacks. It also trains your security teams by letting them respond to fake attacks. This helps them fine-tune their processes and become more effective.
Challenges of CBAS
While CBAS has many benefits, there are also challenges to keep in mind. One of the main challenges is making sure the tests are safe and don't disrupt your live systems. Even though CBAS platforms are designed to be safe, running fake attacks can cause problems if not done carefully. You need to plan carefully and monitor the tests to prevent any harm.
Another challenge is keeping the attack scenarios realistic and up-to-date. The library of attack methods needs to be updated constantly to reflect the latest threats. This requires ongoing research.
Finally, managing the large number of alerts that CBAS can generate can be difficult. You need processes for sorting alerts and prioritizing what to fix first. This often requires cooperation between security, IT, and development teams.
CBAS Best Practices
To get the most out of CBAS, follow these tips. First, understand your most important assets, risks, and threats. Focus your tests on the data, apps, and attack paths that attackers are most likely to target.
Second, integrate CBAS into your security operations. It should be a part of your security system. Make sure the test results are fed into your security tools. This allows your security operations center to respond to fake attacks as if they were real, testing their processes in a controlled way.
Finally, encourage teamwork between security, IT, and development teams. Regular communication makes sure the tests don't disrupt operations and that problems are fixed efficiently. Continuously monitor the tests, adjust the settings to reduce noise, and update the attack scenarios to reflect new threats.
How ImmuniWeb Can Help with Continuous Breach and Attack Simulation?
Outperform traditional one-time penetration tests with 24/7 continuous breach and attack simulation (BAS) by ImmuniWeb® Continuous offering. We continuously monitor and test your web applications and APIs for security vulnerabilities, their exploitability and subsequent data exfiltration by using most relevant TTPs (tactics, techniques and procedures) from MITRE's ATT&CK matrix. Once a security flaw is confirmed, you will be immediately alerted by email, SMS or phone call.
For all customers of continuous breach and attack simulation, we offer a contractual zero false positives SLA and money-back guarantee: if there is a single false positive on your breach and attack simulation dashboard, you get the money back. Our award-winning technology and experienced security experts detect SANS Top 25 and OWASP Top 10 vulnerabilities, including the most sophisticated ones that may require chained, or otherwise untrivial, exploitation.
Leverage our integrations with the leading WAF providers for instant virtual patching of the discovered vulnerabilities. Request to re-test any finding with one click. Ask our security analysts your questions about exploitation or remediation of the findings at no additional cost around the clock. Get a customizable live dashboard with the findings, download vulnerabilities in a PDF or XLS file, or use our DevSecOps integrations to export the continuous breach and attack simulation data into your bug tracker or SIEM.
Disclaimer
The above-mentioned text does not constitute legal or investment advice and is provided “as is” without any warranty of any kind. We recommend talking to ImmuniWeb experts to get a better understanding of the subject matter.











