Cybersecurity is always changing, and attackers are always coming up with new tricks. Red team exercises can be helpful, but they only show you what your security looks like at one point in time. That's why people are starting to use Continuous Automated Red Teaming (CART). It's a way to keep checking and improving your security over time.
What Is Continuous Automated Red Teaming?
Continuous Automated Red Teaming (CART) is like taking traditional red teaming and adding automation and constant monitoring. Instead of doing red team exercises every so often, CART uses tools to pretend to attack your systems and find weak spots all the time. The point is to keep finding problems, testing your defenses, and seeing how well your security team responds in real-time.
This way, you can act like a real attacker who keeps trying to get in. CART platforms try different things, like finding information, exploiting weaknesses, moving around inside your system, and trying to steal data. They do all of this in a safe way. Because it's continuous, CART can immediately start testing for new threats or changes to your systems. This gives you quick feedback on how secure you are.
CART helps you go beyond just checking your security once in a while. It gives you a way to constantly see how strong your defenses are. It helps you find problems before actual attackers do, make sure your security investments are worth it, and keep improving your defenses as new threats come out. By using automation, CART can do things much faster and more often than people can.
Key Aspects of Continuous Automated Red Teaming
CART is all about being continuous and automated. Regular red teaming is usually a one-time thing, but CART platforms are designed to run attack tests all the time, even 24/7. This lets you spot problems and test your defenses as soon as anything changes or new threats appear. Automation lets you test things often and cover a lot of ground, which would be hard to do by hand.
It's also important to copy real-world attack situations. CART isn't just a scanner; it tries to act like actual attackers. It copies the ways they do things, from getting in and finding information to escalating privileges, moving around, and stealing data. CART platforms are always updated with the latest threat information to make sure the attack tests are realistic.
CART also focuses on whether your defenses and security operations are working well. It checks if your security tools are spotting and stopping attacks and if your security team is responding correctly. By running fake attacks all the time, CART gives you good feedback on how well your security team is doing. This helps you improve your security operations and become more resilient.
Why Is Continuous Automated Red Teaming Important?
Continuous Automated Red Teaming is more and more vital because the world of cyber threats is complicated and always changing. Regular tests only show you what your security is like at one moment. But your systems are always changing, with new apps, updates, and vulnerabilities appearing all the time. This means there can be a big gap between tests, which leaves you open to new risks. CART fixes this by giving you constant security checks in real-time.
The number and complexity of cyber threats mean you need to be proactive about security. Attackers are always trying new things. You need a way to keep up with them and continuously test your defenses against the latest attacks. CART platforms copy these threats, so you can be sure your security is working against the most advanced attackers.
CART also helps you see if your security spending is worth it. You put a lot of money into security tools and people. CART shows you whether those investments are actually stopping attacks. It helps you find weak spots and improve your security, so you can be sure you're getting better at defending against threats.
How Does Continuous Automated Red Teaming Work?
Continuous Automated Red Teaming works in several steps, using special platforms. First, you decide what to test and set up the fake attack scenarios. You pick the systems, networks, or apps you want to target. Then, you set up the CART platform with different attack plans that copy how real attackers work. These plans might include phishing, finding information inside your network, exploiting weaknesses, moving around, and stealing data. These scenarios are designed to run all the time in a safe way.
Once it's set up, the CART platform starts running the fake attacks automatically. It uses different tools to look for weaknesses, try to exploit them, and move around the network like an attacker would. This happens continuously, so if you add a new service or change something, the CART system automatically tests it against its library of attack plans.
The system also checks if your defenses are spotting the attacks. As it runs the attacks, the CART platform watches your security tools to see if they detect, alert, and block the attacks. If an attack gets through or isn't detected, the system logs it, noting what was used, what weakness was exploited, and how the attacker got in. This information is put into reports that show you where your defenses are weak. This lets you fix problems, adjust your security tools, and improve your response plans.
Types of Continuous Automated Red Teaming
Continuous Automated Red Teaming can focus on different things. One type is Network-Based CART. This type attacks your network, both inside and outside. It looks for open ports and services, tries to exploit network weaknesses, and simulates moving around inside the network. The goal is to test how well your network is segmented and how well your security systems are working.
Another type is Application-Based CART. This focuses on testing the security of your web apps and other software. It uses tools to copy attacks like SQL injection and Cross-Site Scripting (XSS). This type of CART can be used as you develop and update your apps, so you can be sure you're not adding new weaknesses.
Cloud-Focused CART is used for organizations in cloud environments. This goes beyond regular network and app testing to deal with cloud-specific attacks. It checks for cloud misconfigurations, tries to exploit weaknesses in cloud services, and simulates moving around inside the cloud environment. This is important for making sure your cloud setups are secure against cloud threats.
Components of Continuous Automated Red Teaming
A good Continuous Automated Red Teaming solution has several parts that work together. The Attack Simulation Engine is the main part of the CART platform. It creates and runs realistic, automated attack scenarios. It has a library of attack methods that copy different attacker behaviors. This engine runs the attacks against your systems.
The Target Environment Integration and Discovery Module helps the CART platform understand your IT systems. This part finds your assets and their setups. It connects to your systems, cloud services, and network to get a picture of your attack surface. This lets the CART system adjust its tests as things change.
The Detection Validation, Reporting, and Remediation Orchestration System is an important part of CART. As attacks are run, this part watches your security tools to see if they detect, alert, and block the attacks. It gives you real-time feedback through reports that show you where your defenses are weak. Some CART solutions also connect to ticketing systems and give you advice on how to fix problems.
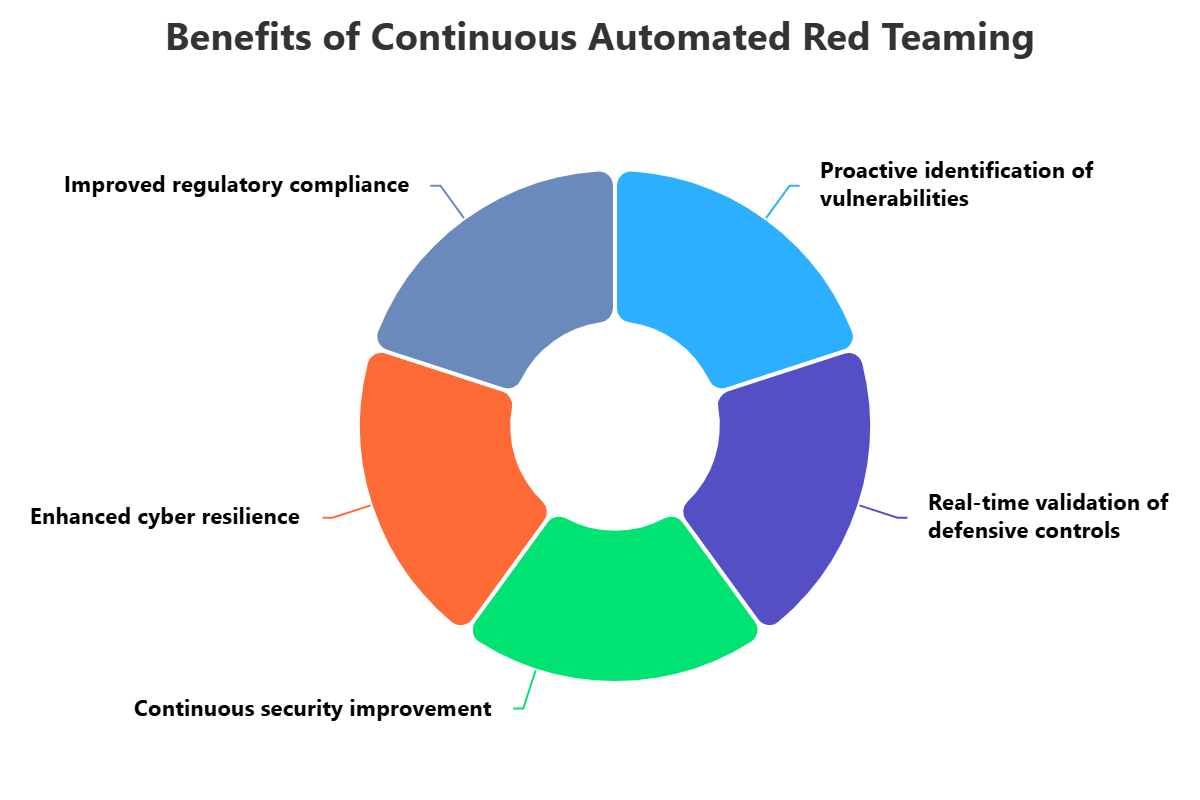
Benefits of Continuous Automated Red Teaming
Continuous Automated Red Teaming has many benefits. It helps you find security gaps and weaknesses early. Unlike regular assessments, CART runs all the time, looking for weaknesses as soon as they appear. This reduces the time you're exposed to threats, so you can fix problems before attackers use them.
It also helps you see if your security investments are worth it. You spend money on security tools and security operations. CART shows you whether those investments are actually working to stop attacks. By running fake attacks and watching how your team responds, CART shows you where your security tools are failing or your policies are weak.
CART also helps you continuously improve your security. The feedback from CART lets your security team learn and adapt quickly. It helps them adjust their tools, improve their detection rules, and improve their response plans. This makes your security stronger and more able to stand up to new threats.
Challenges of Continuous Automated Red Teaming
Even though it has benefits, Continuous Automated Red Teaming also has challenges. One challenge is making the attack simulations realistic while keeping things safe. The attack scenarios need to copy the ways that real attackers work. But running these attacks in a live system needs to be done carefully to avoid causing problems.
Another challenge is dealing with false positives and alert fatigue. A poorly set up system can create a lot of alerts, many of which might not be important. This can make your security team miss real attacks. You need to tune the CART platform to filter out the noise and make sure the alerts are useful.
It can also be hard to connect CART to your existing security tools and workflows. CART platforms need to work with your SIEM and other security solutions to check detection and response. This can be complicated. You also need skilled people to set up, monitor, and adjust the attack scenarios.
Best Practices for Continuous Automated Red Teaming
To get the most out of Continuous Automated Red Teaming, you should follow some best practices. First, understand your important assets and the threats you face. Don't try to automate everything at once. Focus on the most important systems that need continuous checks. Map these assets to the ways that attackers work to make sure your attack simulations are relevant.
Second, create a safe testing environment and set clear rules. CART involves running real attacks. Put safeguards in place to prevent problems. Use a separate testing environment if you can, or make sure the CART platform has controls to limit the impact on your live systems. Keep communication open between the red team, blue team, and other stakeholders.
Finally, focus on feedback, connect to your security operations, and encourage learning. The power of CART is that it gives you immediate feedback on how well your defenses are working. Make sure the alerts and reports from the CART platform go into your security systems so your team can respond quickly. Review the results regularly to adjust your tools, update your rules, and improve your response plans.
How ImmuniWeb Can Help with Continuous Automated Red Teaming?
Outperform traditional one-time penetration tests with 24/7 continuous automated red teaming (CART) by ImmuniWeb® Continuous offering. We continuously monitor and test your web applications and APIs for resilience to advanced hacking techniques, real-life attack scenarios and techniques from MITRE's ATT&CK matrix that are relevant for your industry. Once a security flaw is confirmed, you will be immediately alerted by email, SMS or phone call.
For all customers of continuous automated red teaming, we offer a contractual zero false positives SLA and money-back guarantee: if there is a single false positive on your automated red teaming dashboard, you get the money back. Our award-winning technology and experienced security experts detect SANS Top 25 and OWASP Top 10 vulnerabilities, including the most sophisticated ones that may require chained, multi-step or otherwise untrivial exploitation.
Leverage our integrations with the leading WAF providers for instant virtual patching of the discovered vulnerabilities. Request to re-test any finding with one click. Ask our security analysts your questions about exploitation or remediation of the findings at no additional cost around the clock. Get a customizable live dashboard with the findings, download vulnerabilities in a PDF or XLS file, or use our DevSecOps integrations to export the continuous breach and attack simulation data into your bug tracker or SIEM.
Disclaimer
The above-mentioned text does not constitute legal or investment advice and is provided “as is” without any warranty of any kind. We recommend talking to ImmuniWeb experts to get a better understanding of the subject matter.